Cisco 的解决方案中 PIX VPN的两个问题
nat (dmz) 1 192.168.1.0 255.255.255.0 0 0
route outside 0.0.0.0 0.0.0.0 202.100.100.101 1
route inside 10.1.1.0 255.255.248.0 10.1.3.2 1
route inside 10.1.2.0 255.255.255.0 10.1.3.2 1
timeout xlate 3:00:00
timeout conn 1:00:00 half-closed 0:10:00 udp 0:02:00 rpc 0:10:00 h225 1:00:00
timeout h323 0:05:00 mgcp 0:05:00 sip 0:30:00 sip_media 0:02:00
timeout uauth 0:05:00 absolute
aaa-server TACACS+ protocol tacacs+
aaa-server RADIUS protocol radius
aaa-server RADIUS (inside) host 10.1.3.100 cisco timeout 10
aaa-server LOCAL protocol local
aaa authentication telnet console RADIUS
no snmp-server location
no snmp-server contact
snmp-server community public
no snmp-server enable traps
floodguard enable
sysopt connection permit-ipsec
crypto ipsec transform-set test esp-des esp-md5-hmac
crypto dynamic-map dynmap 10 set transform-set test
crypto map testvpn 10 ipsec-isakmp dynamic dynmap
crypto map testvpn client configuration address initiate
crypto map testvpn client configuration address respond
crypto map testvpn client authentication RADIUS
crypto map testvpn interface outside
isakmp enable outside
isakmp key ******** address 0.0.0.0 netmask 0.0.0.0
isakmp identity address
isakmp nat-traversal 120
isakmp policy 10 authentication pre-share
isakmp policy 10 encryption des
isakmp policy 10 hash md5
isakmp policy 10 group 2
isakmp policy 10 lifetime 86400
vpngroup vpn1 address-pool pool1
vpngroup vpn1 dns-server 202.100.100.198
vpngroup vpn1 default-domain test.cn
vpngroup vpn1 split-tunnel 101
vpngroup vpn1 idle-time 1800
vpngroup vpn1 password ********
vpngroup vpn2 address-pool pool2
vpngroup vpn2 dns-server 202.100.100.198
vpngroup vpn2 default-domain test.cn
vpngroup vpn2 split-tunnel 102
vpngroup vpn2 idle-time 1800
vpngroup vpn2 password ********
telnet 10.1.3.0 255.255.255.0 inside
telnet timeout 5
ssh timeout 5
console timeout 0
terminal width 80
Cryptochecksum:bbafa6e012639b4db524831263ba7b86
: end
注意Cisco VPN Client 低版本(如3.5)在上述环境中使用有问题,须要使用较新的版本,如4.0版本。配置方法为选中VPN连接属性中的“Enable Transparent Tunneling"。
在以上配置中,PIX上有两个vpngroup,均通过本机的地址池分配地址,不同组用户可以访问不同的资源。用户使用不同的Pre-shared key连接PIX,确定其所属的组。用户名、密码则由PIX提交给ACS做集中验证。由于ACS无法限定某个用户只能以某个组的身份登录,如果A组的成员知道了B组的Pre-shared key, 他可以使用自己

route outside 0.0.0.0 0.0.0.0 202.100.100.101 1
route inside 10.1.1.0 255.255.248.0 10.1.3.2 1
route inside 10.1.2.0 255.255.255.0 10.1.3.2 1
timeout xlate 3:00:00
timeout conn 1:00:00 half-closed 0:10:00 udp 0:02:00 rpc 0:10:00 h225 1:00:00
timeout h323 0:05:00 mgcp 0:05:00 sip 0:30:00 sip_media 0:02:00
timeout uauth 0:05:00 absolute
aaa-server TACACS+ protocol tacacs+
aaa-server RADIUS protocol radius
aaa-server RADIUS (inside) host 10.1.3.100 cisco timeout 10
aaa-server LOCAL protocol local
aaa authentication telnet console RADIUS
no snmp-server location
no snmp-server contact
snmp-server community public
no snmp-server enable traps
floodguard enable
sysopt connection permit-ipsec
crypto ipsec transform-set test esp-des esp-md5-hmac
crypto dynamic-map dynmap 10 set transform-set test
crypto map testvpn 10 ipsec-isakmp dynamic dynmap
crypto map testvpn client configuration address initiate
crypto map testvpn client configuration address respond
crypto map testvpn client authentication RADIUS
crypto map testvpn interface outside
isakmp enable outside
isakmp key ******** address 0.0.0.0 netmask 0.0.0.0
isakmp identity address
isakmp nat-traversal 120
isakmp policy 10 authentication pre-share
isakmp policy 10 encryption des
isakmp policy 10 hash md5
isakmp policy 10 group 2
isakmp policy 10 lifetime 86400
vpngroup vpn1 address-pool pool1
vpngroup vpn1 dns-server 202.100.100.198
vpngroup vpn1 default-domain test.cn
vpngroup vpn1 split-tunnel 101
vpngroup vpn1 idle-time 1800
vpngroup vpn1 password ********
vpngroup vpn2 address-pool pool2
vpngroup vpn2 dns-server 202.100.100.198
vpngroup vpn2 default-domain test.cn
vpngroup vpn2 split-tunnel 102
vpngroup vpn2 idle-time 1800
vpngroup vpn2 password ********
telnet 10.1.3.0 255.255.255.0 inside
telnet timeout 5
ssh timeout 5
console timeout 0
terminal width 80
Cryptochecksum:bbafa6e012639b4db524831263ba7b86
: end
注意Cisco VPN Client 低版本(如3.5)在上述环境中使用有问题,须要使用较新的版本,如4.0版本。配置方法为选中VPN连接属性中的“Enable Transparent Tunneling"。
在以上配置中,PIX上有两个vpngroup,均通过本机的地址池分配地址,不同组用户可以访问不同的资源。用户使用不同的Pre-shared key连接PIX,确定其所属的组。用户名、密码则由PIX提交给ACS做集中验证。由于ACS无法限定某个用户只能以某个组的身份登录,如果A组的成员知道了B组的Pre-shared key, 他可以使用自己





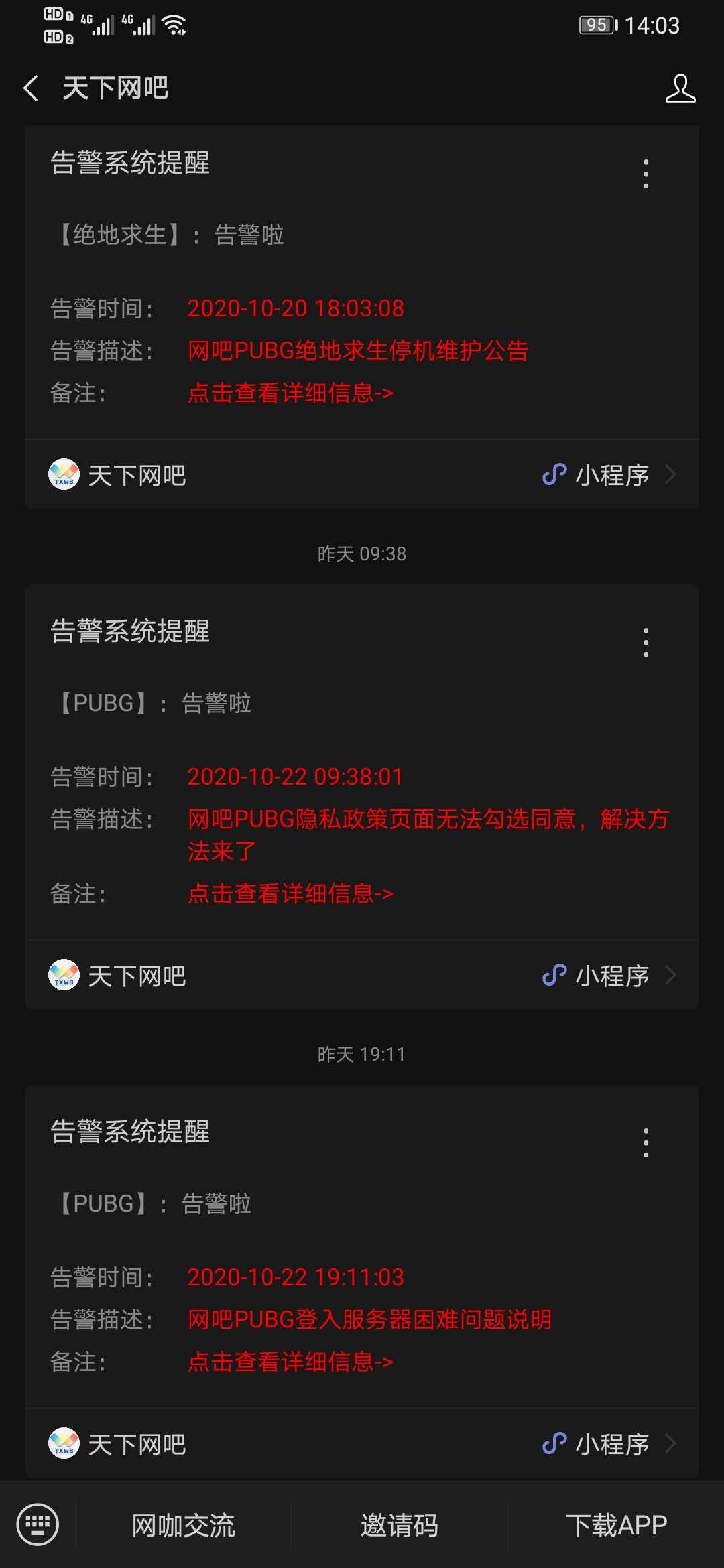
 天下网吧・网吧天下
天下网吧・网吧天下